Museo della Scienza e della Tecnologia “Leonardo da Vinci”, CC BY-SA 4.0, via Wikimedia Commons
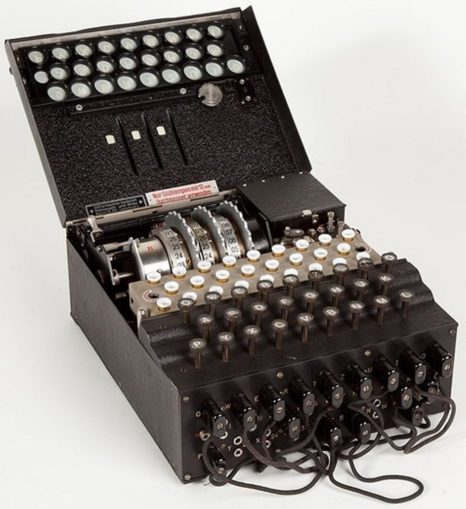
A typical three wheeled Enigma with inspection cover open and showing the three wheels in position. When the Second World War began, three wheels became five.
There is a scene in the film The Imitation Game where Alan Turing (played by Benedict Cumberbatch) and his female assistant Joan Clarke (played by Keira Knightley) are shown standing in front of a large metal cabinet that has rows of discs mounted on its front, turning in unison. Then it stops. The shirt sleeved Turing and maidenly modestly dressed Clark, standing before it then dash towards the camera and begin reading from a small device mounted on a nearby desk. The machine has broken the deadly and complex Enigma cypher. The large cabinet is a faithful copy of a bombe, the code word for an electro mechanical machine devised from ideas developed by Turing for unravelling German messages encoded on the now famous code machine, turning nonsense into plain German.
It is standard practice for films designed to hold an audience, and so make money, to take liberties with history; nearly every Second World War film has done so, many with even greater licence than in this present example. For it was quite impossible for the bombe to produce a decode. Turing did not have that within even his great mathematical powers. Today a single message enciphered on an Enigma, with no pre-existing clues as to its content, would present a challenge to a super computer running at several millions of bits a second rather than as with the 1940s era bombe ticking round at a sedate pace checking individual characters one at a time.
It would be a challenge of another kind and as time consuming to present a complete explanation of the processes that led to Allied success against Enigma. There is no drama to be had in showing someone thinking for months on end and precious few ways to show this speeded up that aren’t on the level of one alleged filmic moment seeking to speed up historical events: ‘Hello Lenin! I’m Trotsky. Isn’t that Stalin standing over there?’
The explanation for the distortion of history in the re-imagined breakthrough scene is that Turing’s concept for attacking the cyphers produced by the Enigma was not to decrypt such a message in one go but to render it possible for a human being to do so. Not so much of a eureka moment.
The human brain is simply astonishing. In successfully completing a crossword of even modest difficulty, the mind has had to accomplish the task of discarding millions upon millions of possibilities using intuition alone. It is a common mistake to believe machines can read. Only human beings can read. Reading is not even possible to explain for the most part; it’s in the realm of conjecture as to how children learn to read by associating sounds with characters arranged in a certain order, leaving aside meaning and comprehension. Machines, computers, can however be programmed to do sorting at speeds that are unimaginably faster than a human being and without limit of physical exhaustion. They can be set up to look for collections of characters related to strings of code from which a word is formed. Computers can seek out and compare patterns that relate to meaning at unimaginable speed. Yet, no machine reads in the sense of understanding what it is doing or has done. Only humans can do this. Significantly, computers play chess but none have been proposed that could complete a crossword.
It is not known for certain – it is unknowable – if Turing was the first person to notice that Enigma machines could never turn a plaintext letter in a message back into itself. However many times one depresses any one of its keys, the letter that illuminates at the light panel atop of the keyboard is never itself: K never becomes K. If the Germans had noticed then they had not apparently thought this a serious weakness. But Turning did and so did the people responsible for Britain’s own wartime code machine. Typex, itself based on the original Enigma machine, but with mechanical additions that occasionally permitted a letter to be enciphered as itself at near random intervals. This posed a serious developmental complication – the British wasted years deciding what kind of cypher machine they required – that would have only have been untaken I suggest if the flaw that gave Turing his insight had been observed beforehand. Whatever the case, Turning knew it to be a fatal flaw. But there were no machines at Bletchley or anywhere else where gobbledygook went in one end and perfect German came out at the other.
It is a commonplace in some studies (there must now be hundreds that have made it into print) and much online chatter that suggests the British stole the limelight for breaking ’the’ Enigma code machine from the Polish. That is a falsehood, maybe something worse. When the Enigma story emerged in 1978, a B.B.C. series Secret War broadcast soon afterwards ended with the then known details of the breakthrough that ‘altered the course of the Second World War’, without however mentioning Turing or any Bletchley personnel. But it did carry an on screen tribute to the three young Polish cryptanalysts delivered by the somewhat austere figure of Dr R. V. Jones, Churchill’s wartime scientific adviser, a man who gave this viewer the impression he was quite aware of his own self worth. The Poles were acknowledged from the start. But others today wish to place the British in a poor light where national success is concerned. Nothing new.
Jerzy Rozycki, Henryk Zygalski and Marian Rejewski were all very young and had studied mathematics at Poznan university, and recruited by the Polish General Staff’s Cypher Bureau in Warsaw in the early 1930s. Of the three Rejewski is the most credited with feat of breaking Enigma. The British, French, possibly Americans had cypher departments that had many successes and the skill up to a point, but none had succeeded with Enigma. The novelty of the Polish approach was it relied upon mathematics where the rest had not made that transition from attacks based on linguistic ideas. Besides, incredible in hindsight , no one thought there would be a war, a view even shared by some of German’s own non-Nazi High Command before the Austrian Corporal got his feet well an truly under the German table.

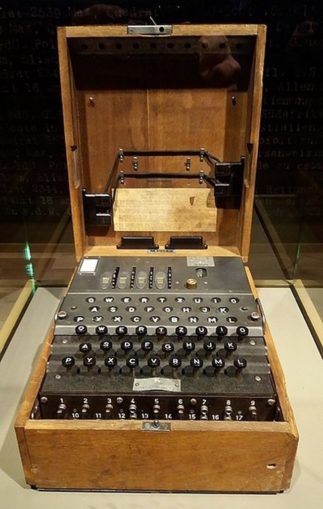
No photographer mentioned in either source, Public domain, via Wikimedia Commons
The crack in German security appeared quite early on in the person of Hans Thilo Schmidt, a womanising, drunk and gambler – so an ideal person to entrust with a great secret; there does seem to be an employment pattern in intelligence circles. Schmidt had got a job through his family connections that gave him access to the codes and so, in short, wanted cash for his expensive habits. He had tried to sell Enigma settings, what we would call ‘software’ today, to several countries but was apparently turned down by them all. The Poles where his last chance. The Poles, stuck between Germany and Russia wanted to survive. They got materials from Schmidt and even ‘borrowed’ an Enigma machine sent through the diplomatic mail and copied it. However, the cunning head of the Polish intelligence arm charged with breaking into German Enigma traffic did not share the details so obtained with his young team; he wanted them to work from first principles. That way they would ‘own’ any results and be better prepared to counter changes that would inevitably come along in due time.
The team examined a Polish Enigma machine copied for the industrious Polish intelligence staff. After a long period of conjectures and refutations, Rejewski noted almost in passing a feature of encrypted Enigma messages, whereby he was able to make links of certain lengths such as e.g. 9, 7, 5, 5, four self contained groups of characters. He realised this was a sort of finger print created by the arrangement of wheel working together in a particular order. In short if the three wheels were placed together in a certain order in the Enigma used for that day’s traffic, they left this pattern. Rejewski set his tiny team to laboriously work through all the permutations (26x26x26x6) of the three rotors, slowly building a catalogue so that, eventually, when a message was intercepted he could look up the counts of groups in the catalogue and instead of many millions of possibilities reduce these to a smaller number for examination by hand. When, in 1938 and Hitler’s coveted war for more German living space was clearly in the offing, the German military added more wheels to the basic Enigma to increase the number of permutations and changed the ‘wheel order’ daily rather than only after weeks, as had happened previously. The group technique would not work without an immense new effort that was beyond the heroic Poles; the time cost of finding and testing the wheel order using the former method would not be feasible with their resources. However, the Poles fought back. Rejewski made a start with mechanization, a series of linked ‘enigmas’ in a configuration that would test a hypothesis derived from logic and known characteristics of the machine and the German language. Using a machine to break another machine. He called his mechanical device a ‘bomba’ after a iced cream confectionary he had been consuming when he had his idea. He had in effect designed a sort of early ‘search engine’. This he showed to both the British and French intelligence services on the eve of Hitler’s war.
Turing’s ‘bombe’, so named in homage to the Poles, used a very simple but powerful idea of eliminating all the Enigma wheel settings that the message could not have used through the power of contradiction. In this he used a idea that every falsehood confirmed a truth. Since no character typed into an Enigma could become itself it stood to reason that a string which resulted in A – F – J – A is ’illegal’. The Enigma would be incapable of such a swapping procedure, therefore the conjecture being examined was wrong and the bombe would mechanically skip to the next wheel setting in turn and try again. At the end of this process if all went well, a set of possibilities would be presented at the end of a ‘run’. Instead of 60 (5x4x3) wheel orders to examine, the figure would have been reduced to a few candidates. These could then be examined using copies of Enigma (supplied by the Poles initially) held at Bletchley Park. If the correct wheel order had been found (by no means always the case), the result would produce a string of characters that to the average person would look just so much gobbledygook as the original message. (cue Mr Cumberbatch and Miss Knighley) But to the trained eyes of code breakers a non random pattern would be apparent. Patterns are the downfall of codes. Like an old inscription being cleaned of centuries of dust and dirt – something a few scholars at Bletchley had had experience of no doubt – fragments of German words would emerge. Just as with the skill of a practiced crossword puzzler, these fragments would become a message.
Turning had separated the keyboard part of Enigma from the plugboard and the millions and millions of ways the twenty six letters of the alphabet can be arranged (26x25x24 … or 26!). What seemed to be the invincible core of the encypherment process could be bypassed with something like ease. Yet, the messages so revealed in plaintext could be less than useless in themselves. The clever part was record keeping. It was the key to exploiting the Enigma break.
The process of exploiting a message went on in a well organised, one might say industrial, fashion. One of the very great achievements of Bletchley Park was in collating, messages, noting key words, service names, place names and unit details in an archive of information. As the archive grew it could be ‘consulted’ using punch card sorting machines to look at connected material and to compile an expanding intelligence ‘picture’. A simple ‘movement order’ for a Luftwaffe officer technical specialist from one unit to another much further away might reveal a forthcoming offensive. The scanning intelligence officers might detect growing problems and shortages not apparent in just a single message but taken with others, and a current understanding of the enemies stance, tactical information of great use.
Tactical rather than strategic. For strategic information did come through an even more astounding Bletchley triumph, one entirely their own. To describe that even in bare outlines goes beyond this essay on Enigma to an even greater intellectual feat. A story for another time.
Each wireless network had separate daily and monthly keys and settings. Fewer networks using the Enigma code were broken or even attacked than most people realise. There were too many and so the British sensibly concentrated on just those that would be the most useful to exploit. Some networks exercised strict code discipline and were never broken. For long periods no breaks came even on networks Bletchley had had success against; the early bombes did not work very reliably. The deadliest instance a a blackout was when the U boat traffic began using a unique to that service four wheeled Enigma that resulted in a signals blackout for ten months in 1942, resumed only after heroics at sea by the Royal Navy and the capture of U 559’s code books. (Contrary to Hollywood’s imaginative leaps e.g. U571, possessing a code machine is helpful but not essential. Bletchley reconstructed the mechanics of coding machines it never saw simply by examining the cypher stream.)
Some historians recently have queried whether the contribution of the Enigma break was as crucial as is claimed; there were other technical and scientific breakthroughs that were equal to code breaking – advanced British high frequency radio detection for example, ‘Huff Duff’, used to hunt down U boats with great success; airborne radar H2S, or, wireless traffic analysis invented in detail at Bletchley. Not least plugging gaping holes in Allied signals, amply and expertly exploited by the Germans. Will we ever know the honest answer to that query? However, the enemy was utterly defeated, and much sooner than many dared hope.
Several major and minor books have been consulted in writing this piece – which is in no wise comprehensive. I recommend the following authors who can be researched online by name: Ralph Erskine, Jack Copeland, F. H. Hinsley, Alan Stripp, Michael Smith, Hugh Sebag Montefiore. Others such as Simon Singh have written informative pieces. Andrew Hodges’ biography of Alan Turing is a sight better than most later works.
LukaszKatlewa, CC BY-SA 3.0, via Wikimedia Commons
© Larkers A.D. 2021
The Goodnight Vienna Audio file